Conditional Access for the real world
Security AND accessibility at the same time
I recently spoke at Microsoft Ignite: The Tour about Conditional Access in Azure Active directory and how many organisations tend to block access for their users. This post series is a review of the main takeaways from that talk.

In today’s cloud-driven, software as a service productivity working environment, IT administrators have to find a balance between security and productivity. Users want to be able to do their work from any device, connected to any internet connection from anywhere in the world. But it’s your job to make sure the organisation’s data is secured.
In 2016 Microsoft introduced the concept of Conditional Access.
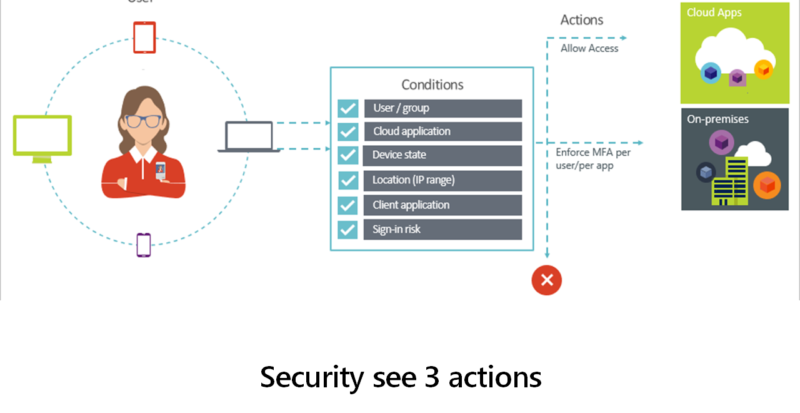
Conditional Access is the tool used by Azure Active Directory to bring signals together, to make decisions, and enforce organizational policies.
https://docs.microsoft.com/en-us/azure/active-directory/conditional-access/overview

So what the marketing images (like the one above) did, was portray this new system as being a way to either allow our users into the service, require Multi-factor Authentication (MFA) or block the bad guys. That’s great but what IT security saw was the ability to restrict users and make their lives more difficult, by securing the organisation but not allowing the users to be productive from any device, anywhere in the world.

In reality though, there are lots of conditions one can interpret and many more controls.
Don’t just block
Three things, other than block, that you can do with Conditional Access:
1. Require MFA from untrusted network

Stay tuned for 2. “Restrict SharePoint to read only when access from unmanaged device”, 3. Proxy application through Microsoft Cloud App Security (MCAS), best practices and some common Conditional Access policies…
In the meantime, check out my latest post about “Conditional Access for Office 365 – What an admin needs to know” on the ENow Software blog, and while you are there take a look at their monitoring software for Office 365, it provides a single pane of glass across your on premises, hybrid, Office 365 workloads and your remote locations

One comment